Exhibit
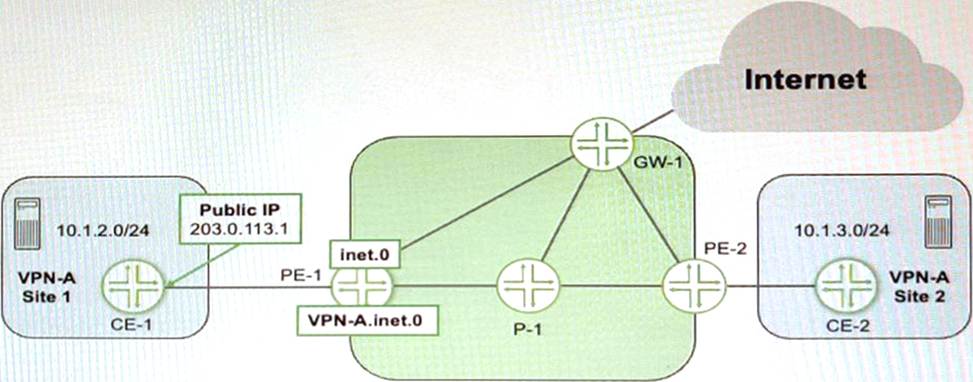
Referring to the exhibit, CE-1 is providing NAT services for the hosts at Site 1 and you must provide Internet access for those hosts
Which two statements are correct in this scenario? (Choose two.)
A. You must configure a static route in the main routing instance for the 10 1 2.0/24 prefix that uses the VPN-
B. inet.0 table as the next hop
C. You must configure a static route in the main routing instance for the 203.0.113.1/32 prefix that uses the VPN-
D. inet.0 table as the next hop.
E. You must configure a RIB group on PE-1 to leak a default route from the inet.0 table to the VPN-
F. inet.0 table.
G. You must configure a RIB group on PE-1 to leak the 10 1 2.0/24 prefix from the VPN-
H. inet.0 table to the inet.0 table.
Explanation:
In the given scenario, where CE-1 at Site 1 is providing NAT services and requires Internet access for its hosts, the correct configuration on PE-1 to provide Internet access involves routing and potentially using Routing Information Base (RIB) groups to ensure proper route leaking between VRFs (Virtual Routing and Forwarding instances) and the global routing table. Here are the correct statements:
You must configure a RIB group on PE-1 to leak a default route from the inet.0 table to the VPN-A.inet.0 table. By leaking a default route into the VPN-A routing table, hosts in Site 1 will be able to access the Internet via the PE-1 gateway. This is assuming that PE-1 is the gateway to the Internet for the VPN-A site.
You must configure a RIB group on PE-1 to leak the 10.1.2.0/24 prefix from the VPN-A.inet.0 table to the inet.0 table. This step is necessary if other devices in the main routing instance need to reach the hosts behind CE-1, which are performing NAT. This allows for return traffic from the Internet destined for the NATed IP addresses to find the correct route back to the CE-1 device.